
Security News
Axios Maintainer Confirms Social Engineering Attack Behind npm Compromise
Axios compromise traced to social engineering, showing how attacks on maintainers can bypass controls and expose the broader software supply chain.
command-line-args
Advanced tools
Upgraders, please read the release notes
A mature, feature-complete library to parse command-line options.
You can set options using the main notation standards (learn more). These commands are all equivalent, setting the same values:
$ example --verbose --timeout=1000 --src one.js --src two.js
$ example --verbose --timeout 1000 --src one.js two.js
$ example -vt 1000 --src one.js two.js
$ example -vt 1000 one.js two.js
To access the values, first create a list of option definitions describing the options your application accepts. The type property is a setter function (the value supplied is passed through this), giving you full control over the value received.
const optionDefinitions = [
{ name: 'verbose', alias: 'v', type: Boolean },
{ name: 'src', type: String, multiple: true, defaultOption: true },
{ name: 'timeout', alias: 't', type: Number }
]
Next, parse the options using commandLineArgs():
import commandLineArgs from 'command-line-args'
const options = commandLineArgs(optionDefinitions)
options now looks like this:
{
src: [
'one.js',
'two.js'
],
verbose: true,
timeout: 1000
}
Beside the above typical usage, you can configure command-line-args to accept more advanced syntax forms.
Command-based syntax (git style) in the form:
$ executable <command> [options]
For example.
$ git commit --squash -m "This is my commit message"
Command and sub-command syntax (docker style) in the form:
$ executable <command> [options] <sub-command> [options]
For example.
$ docker run --detached --image centos bash -c yum install -y httpd
A usage guide (typically printed when --help is set) can be generated using command-line-usage. See the examples below and read the documentation for instructions how to create them.
A typical usage guide example.

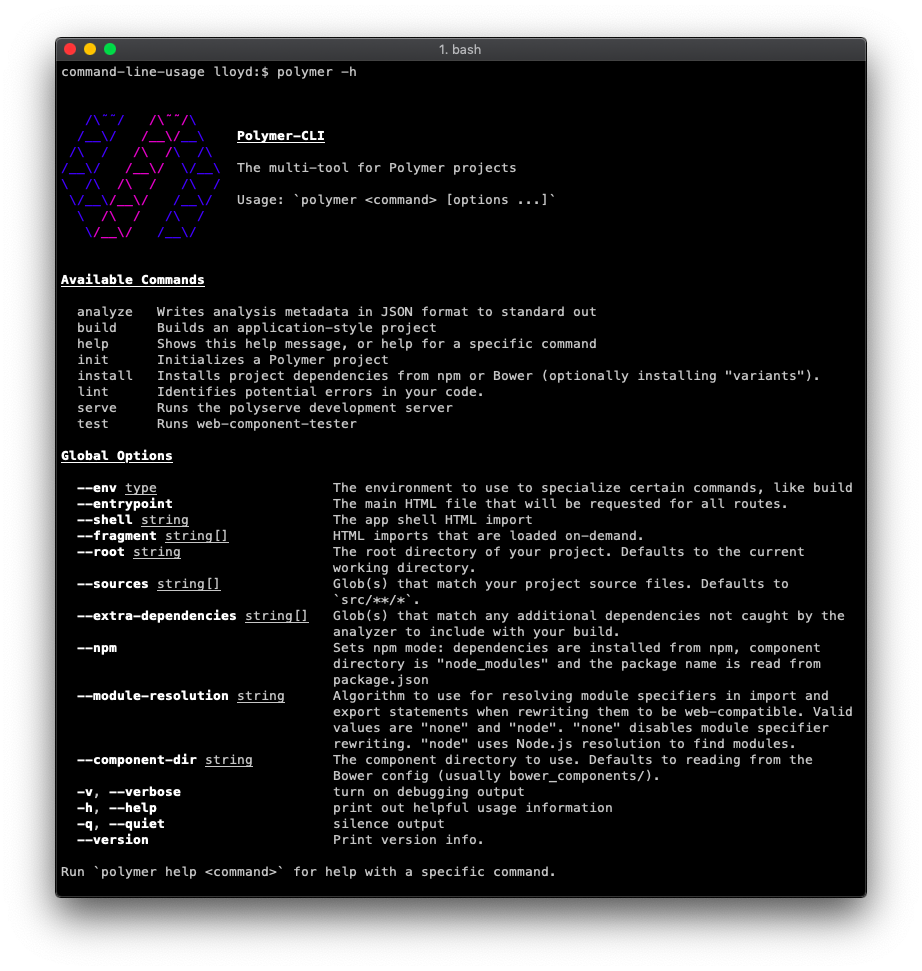
The polymer-cli usage guide is a good real-life example.
There is plenty more to learn, please see the wiki for examples and documentation.
$ npm install command-line-args --save
© 2014-26 Lloyd Brookes <opensource@75lb.com>.
Documented by jsdoc-to-markdown.
Yargs is a popular library for parsing command-line arguments in Node.js. It provides a rich set of features, including command handling, argument validation, and automatic help generation. Compared to command-line-args, yargs offers more advanced features and a more user-friendly API.
Commander is another widely-used library for building command-line interfaces in Node.js. It supports option parsing, command definitions, and automatic help generation. Commander is known for its simplicity and ease of use, making it a good alternative to command-line-args for simpler use cases.
Minimist is a lightweight library for parsing command-line arguments. It provides basic functionality for handling options and arguments, but lacks some of the advanced features found in command-line-args, yargs, and commander. Minimist is a good choice for projects that require minimal overhead.
FAQs
A mature, feature-complete library to parse command-line options.
The npm package command-line-args receives a total of 4,449,808 weekly downloads. As such, command-line-args popularity was classified as popular.
We found that command-line-args demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Axios compromise traced to social engineering, showing how attacks on maintainers can bypass controls and expose the broader software supply chain.

Security News
Node.js has paused its bug bounty program after funding ended, removing payouts for vulnerability reports but keeping its security process unchanged.

Security News
The Axios compromise shows how time-dependent dependency resolution makes exposure harder to detect and contain.